The First International Standard in the Field of LLM Supply Chain Security: Interpretation of WDTA’s Large Language Model Security Requirements for Supply Chain
2024-09-09 17:48:00
On September 6th, the World Digital Technology Academy (WDTA) officially released the international standard Large Language Model Security Requirements for Supply Chain at the 2024 Bund Summit. This standard proposes a systematic framework for managing security risks in the supply chain of Large Language Models (LLMs), covering the entire lifecycle of LLMs—from development and training to deployment and maintenance—and providing detailed guidance for each stage.
I. Background of the Standard’s Release
The development of artificial intelligence systems, particularly Large Language Models (LLMs), has penetrated various industries, including healthcare, finance, transportation, and more. While these models drive innovation and convenience, they also bring increased security risks. As the development and deployment of LLMs typically rely on complex global supply chains, any link in these chains may become a potential source of security vulnerabilities. To ensure the safety and stability of LLMs, experts from dozens of organizations (including CSA Greater China, Ant Group, Microsoft, Google, Baidu, NIST, Meta, PrivateAI) jointly compiled the Large Language Model Security Requirements for Supply Chain standard. It aims to help organizations identify and manage supply chain security risks.
II. Challenges in LLM Supply Chain Security
Compared with traditional supply chains, LLM supply chains involve numerous software components, data resources, third-party services, and development tools, thus facing more complex security challenges. These challenges mainly include:
- Supply chain complexity: The training, deployment, and application of LLMs depend on a large number of open-source components, third-party tools, and distributed computing architectures, expanding the attack surface.
- Data privacy and compliance issues: LLM training requires massive datasets, and ensuring secure data transmission and storage remains an ongoing challenge.
- Multi-party collaboration risks: In global supply chains, suppliers from different countries/regions may adopt varying security standards, increasing collaboration uncertainties.
- Intrinsic model security risks: During LLM training, deployment, and application, models may face risks of attack, tampering, or exploitation (e.g., adversarial attacks).
III. Scope of the Standard
The Large Language Model Security Requirements for Supply Chain establishes a supply chain security protection framework for LLMs. It sets out requirements for managing supply chain security risks and activities in LLM development, operation, and maintenance (O&M), and provides information on common supply chain security risks and typical cases.
The standard can guide suppliers/consumers in security risk assessment and supply activity management, and serve as a basis for third-party organizations to conduct supply chain security testing/evaluation for regulators.
IV. Detailed Introduction to the Standard’s Content
The core of the Large Language Model Security Requirements for Supply Chain emphasizes a multi-layered security approach (covering the network layer, system layer, platform/application layer, model layer, and data layer). It leverages key concepts (Machine Learning Bill of Materials [ML-BOM], zero-trust architecture, continuous monitoring and auditing) to ensure LLM system integrity, availability, confidentiality, controllability, and reliability throughout the supply chain.
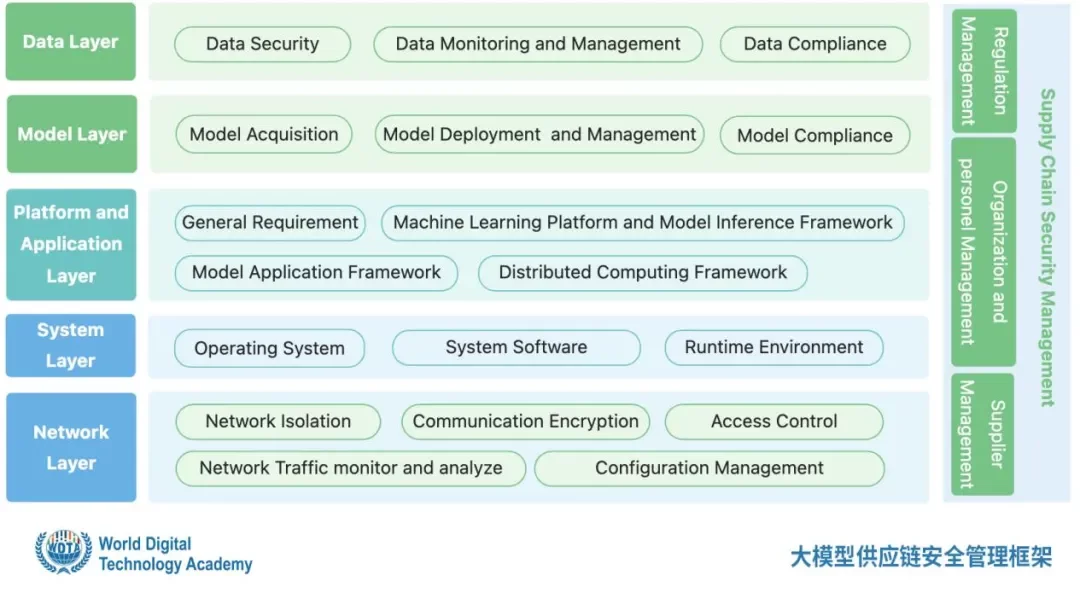
WDTA LLM Supply Chain Security Framework
01 Network Layer Security Requirements
- Isolate critical networks: Mandate physical and logical isolation of critical data/systems from external networks to reduce attack surfaces and prevent sensitive information leakage.
- Encrypted transmission: Require encryption for all critical data transmission to ensure confidentiality and integrity.
- Access control: Implement strict access control for critical network information/services and retain access logs for traceability.
02 System Layer Security Requirements
- Operating system security: Stress timely OS updates and patches to avoid exploitation of known vulnerabilities.
- System software security: Ensure system software comes from trusted sources and is verified via digital signatures before deployment.
- Runtime environment security: Use virtualization/containerization technologies to create independent isolated environments for each application and reduce risks.
03 Platform and Application Layer Security Requirements
- Third-party component management: Recommend strict control of third-party component sources/versions, security assessment before use, and timely updates.
- Model inference framework security: Require security analysis of model files in deployment to prevent malicious exploitation during runtime.
- Model application framework security: Avoid storing model call interface keys in code; adopt security isolation for code execution tools (e.g., code interpreters).
- Distributed computing framework permission verification: Implement permission verification between root and child nodes to prevent unauthorized access.
04 Model Layer Security Requirements
- Model file security: Obtain model files from trusted third parties and conduct integrity checks before use to prevent tampering/malicious code implantation.
- Model behavior monitoring: Use monitoring tools for real-time model behavior monitoring after deployment to detect and respond to anomalies promptly.
05 Data Layer Security Requirements
- Data classification and grading: Classify data by importance/sensitivity and adopt corresponding security measures for storage/transmission.
- Encryption and backup: Require encryption of critical data and regular backups, and establish effective disaster recovery plans.
- Data compliance auditing: Audit third-party-provided data and comply with relevant laws/regulations to ensure data source legality and prevent abuse.
V. Continuous Improvement of Supply Chain Security Management
- Formulate management systems: Require enterprises to develop comprehensive supply chain security management systems (covering risk, supplier, personnel, and compliance management) to ensure transparency and controllability.
- Supplier management: Conduct strict supplier selection and continuous evaluation to ensure product/service authenticity/integrity and prevent information tampering/leakage.
- Continuous monitoring and improvement: Implement continuous security monitoring across all supply chain links, conduct regular risk assessments and improvements to address evolving threats.
The Large Language Model Security Requirements for Supply Chain provides clear guidance for building a more secure AI ecosystem by defining multi-layered supply chain security requirements. It aims to enhance enterprise AI deployment security and reliability (both technically and managerially). We encourage AI supply chain stakeholders to actively adopt this standard to jointly build a safe, trustworthy, and sustainable future AI environment.




Programs & Initiatives
Events
Research & Publications
Awards & News